Angler Exploit Kit, Bedep, and CryptXXX
Introduction
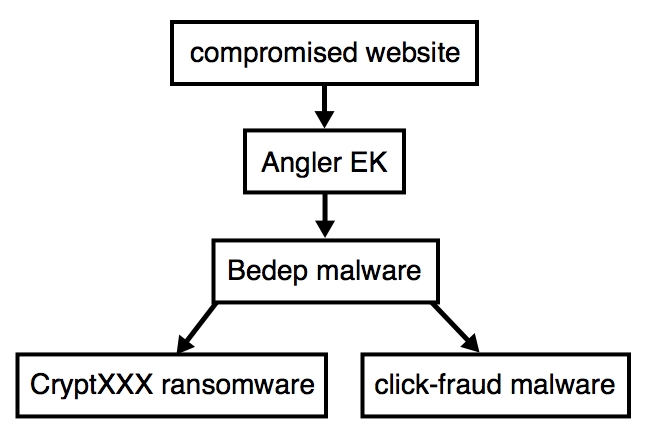
On Friday 2016-04-15, Proofpoint researchers spotted CryptXXX [1], a new type of ransomware from the actors behind Reveton. CryptXXX is currently spread through Bedep infections sent by the Angler exploit kit (EK). So far, I've only seen Bedep send CryptXXX after Angler EK traffic caused by the pseudo-Darkleech campaign. The chain of events is illustrated below:
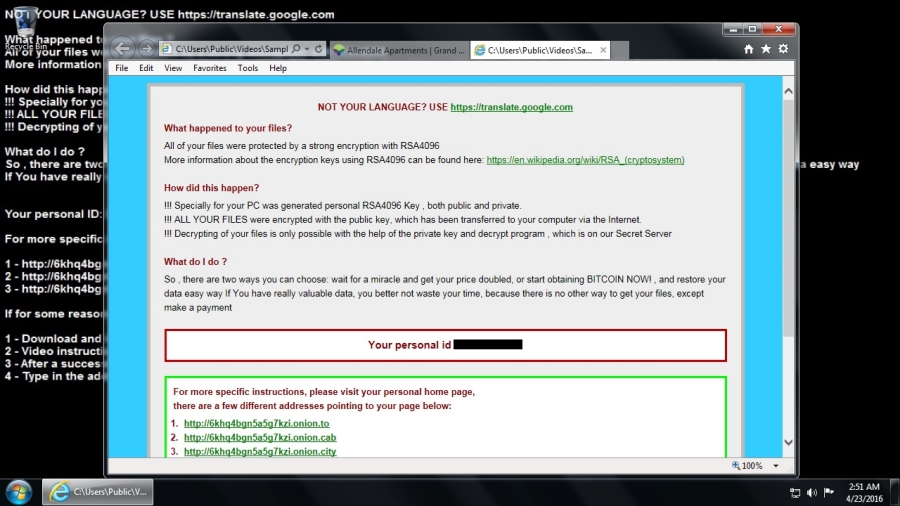
CryptXXX infections have their own distinct look. Below is an image of a Windows 7 desktop after an Angler EK/Bedep/CryptXXX infection from Saturday 2016-04-23 [2]:
Bedep recently improved its evasion capabilities [3]. It's being sent by one of the most capable EKs on the criminal market, and now we're seeing a new type of ransomware. Let's take a look at traffic from this Angler EK/Bedep/CryptXXX combo.
Details
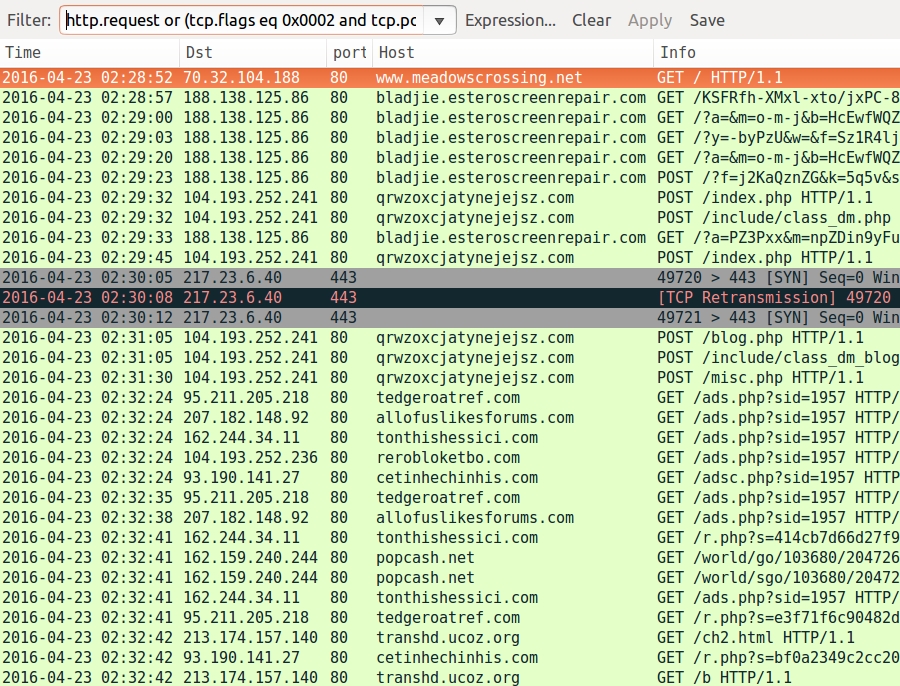
Below is an image of traffic filtered in Wireshark from an Angler EK/Bedep/CryptXXX infection on 2016-04-23. I used the Wireshark filter http.request or (tcp.port eq 443 and tcp.flags eq 0x0002) to also check for CryptXXX callback traffic as described in the Proofpoint blog.
The first HTTP request is for the compromised website. Next, we see the following indicators of compromise (IOCs):
- 188.138.125.86 port 80 - bladjie.esteroscreenrepair.com - Angler EK
- 104.193.252.241 port 80 - qrwzoxcjatynejejsz.com - Bedep post-infection traffic
- 217.23.6.40 port 443 - CryptXXX ransomware callback traffic (encrypted)
- 93.190.141.27 port 80 - cetinhechinhis.com - Traffic from the click-fraud malware
- 95.211.205.218 port 80 - tedgeroatref.com - Traffic from the click-fraud malware
- 104.193.252.236 port 80 - rerobloketbo.com - Traffic from the click-fraud malware
- 162.244.34.11 port 80 - tonthishessici.com - Traffic from the click-fraud malware
- 207.182.148.92 port 80 - allofuslikesforums.com - Traffic from the click-fraud malware
As usual with the pseudo-Darkleech campaign, we find a distinctive pattern of injected script in a page from the compromised website. Daniel Wesemann, another ISC handler, has posted a step-by-step example for decoding this type of script (in two parts: part 1 and part 2).
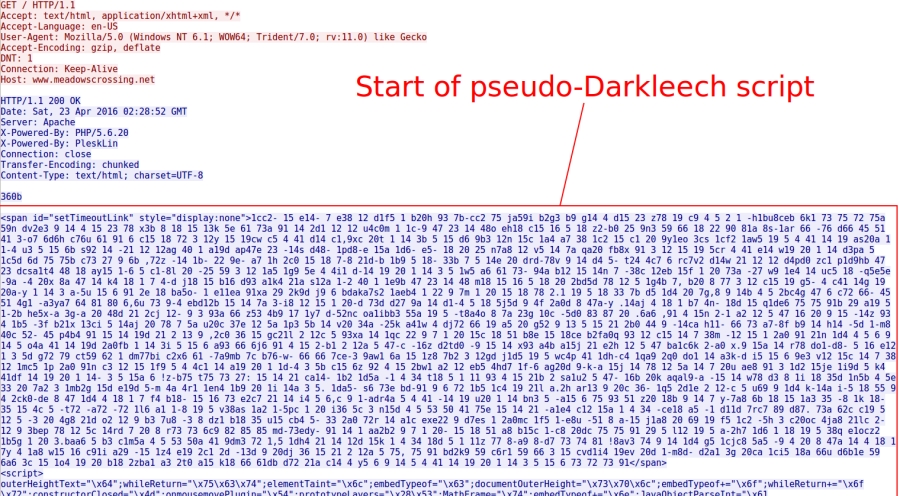
Shown above: Start of injected pseudo-Darkleech script sent by the compromised site.
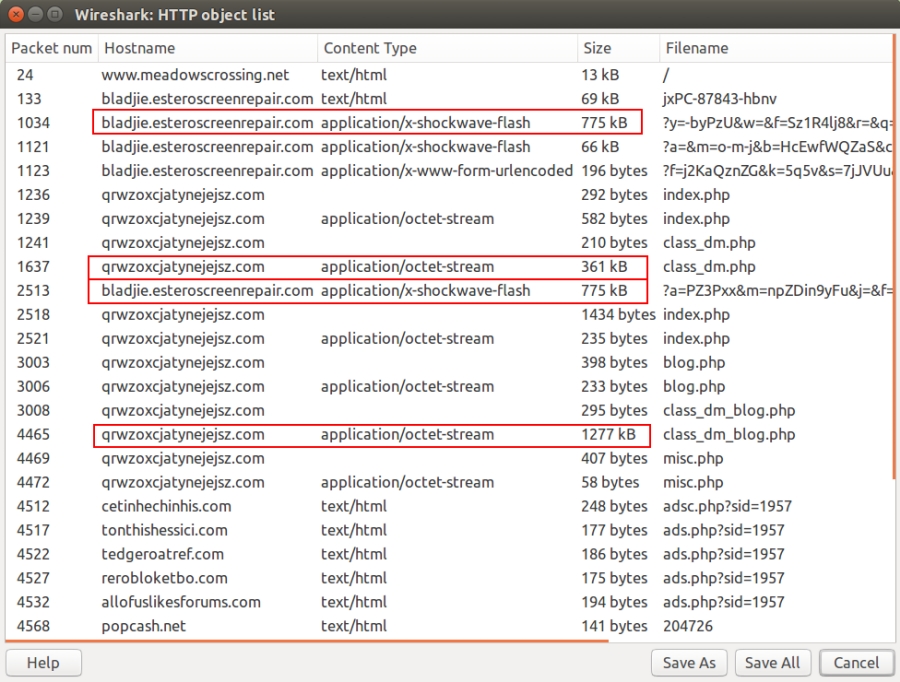
Aside from a few URL pattern changes, Angler EK remains recognizable. However, Angler EK now masquerades its payload as a Flash file [4]. But it's not actually Flash. It's the same kind of encrypted payload data as before, just disguised as a Flash file. As always, this gets decrypted on the victim's Windows computer.
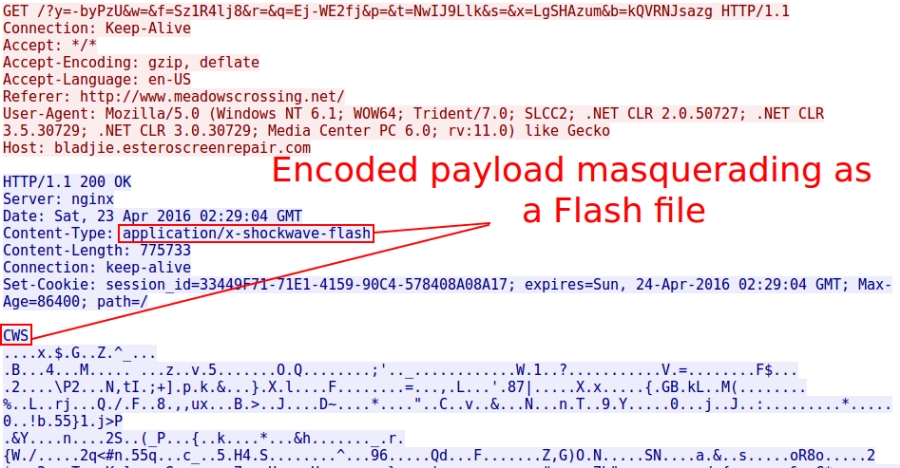
Shown above: Angler EK masquerading the encrypted payload as a Flash file.
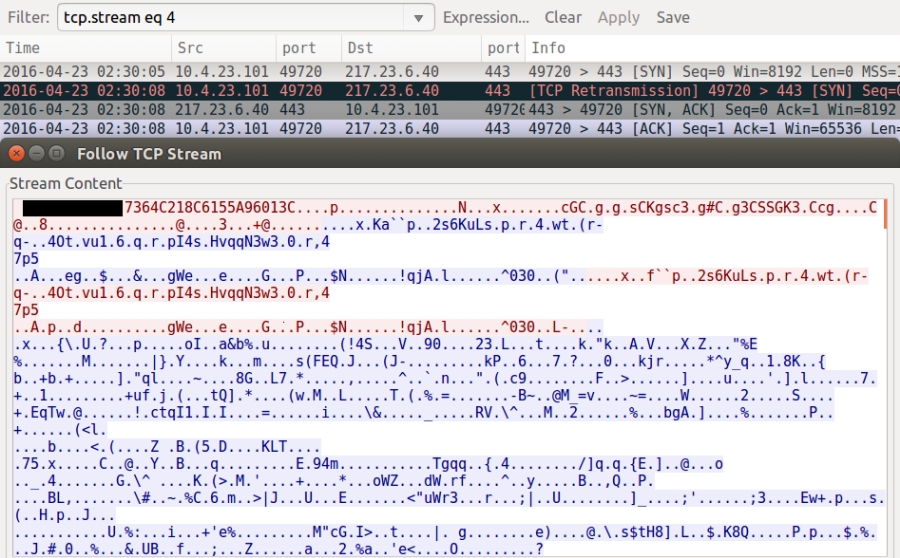
As Proofpoint's blog post already noted, CryptXXX uses a custom protocol on TCP port 443 for its callback traffic. Below is an example.
Since this is a fileless infection (an old Angler trick), Bedep is stored in memory. You won't find it on the infected host. But the traffic always provides clues. When looking at the traffic in Wireshark, use File --> Export Objects --> HTTP. In that list, you'll see where Angler EK sends the encrypted Bedep payload (disguised as a 775 kB Flash file). You can also find Bedep downloading encoded data for both CryptXXX (361 kB) and the click-fraud malware (1277 kB).
Artifacts left behind on the infected Windows host include:
- C:\ProgramData\{9A88E103-A20A-4EA5-8636-C73B709A5BF8}\8afc49b02429a
- C:\ProgramData\{9A88E103-A20A-4EA5-8636-C73B709A5BF8}\msvcp60.dll
- C:\ProgramData\3A1DC4C4719C.dat
- C:\Users\Public\Music\Sample Music\de_crypt_readme.bmp
- C:\Users\Public\Music\Sample Music\de_crypt_readme.html
- C:\Users\Public\Music\Sample Music\de_crypt_readme.txt
- C:\Users\Public\Pictures\Sample Pictures\de_crypt_readme.bmp
- C:\Users\Public\Pictures\Sample Pictures\de_crypt_readme.html
- C:\Users\Public\Pictures\Sample Pictures\de_crypt_readme.txt
- C:\Users\Public\Videos\Sample Videos\de_crypt_readme.bmp
- C:\Users\Public\Videos\Sample Videos\de_crypt_readme.html
- C:\Users\Public\Videos\Sample Videos\de_crypt_readme.txt
- C:\Users\[username]\AppData\Local\Temp\{F4DD9BAF-BD38-4055-90EE-07C071479B6A}\api-ms-win-system-acproxy-l1-1-0.dll
The top group is related to click-fraud malware. The bottom group is related to CryptXXX ransomware. Both were saved as DLL files.
Final words
This diary doesn't reveal anything new for Angler EK/Bedep/CryptXXX. However, I believe this combination is a significant development in EK-sourced ransomware. It deserves more scrutiny. Hopefully, repeated exposure will keep everyone aware of this continuing threat.
Pcap and malware for today's diary can be found here. Earlier examples are available at:
- http://malware-traffic-analysis.net/2016/04/18/index.html
- http://malware-traffic-analysis.net/2016/04/20/index.html
- http://malware-traffic-analysis.net/2016/04/22/index.html
---
Brad Duncan
brad [at] malware-traffic-analysis.net
References:
[1] https://www.proofpoint.com/us/threat-insight/post/cryptxxx-new-ransomware-actors-behind-reveton-dropping-angler
[2] http://malware-traffic-analysis.net/2016/04/23/index.html
[3] http://malware.dontneedcoffee.com/2016/04/bedepantiVM.html
[4] https://twitter.com/kafeine/status/718449401396654080

Comments
Anonymous
Apr 25th 2016
8 years ago
Anonymous
Apr 26th 2016
8 years ago
Contacting the abuse departments of the hosting providers and registrars often works, but the sites are active until that happens, and a lot of damage can be done in the meanwhile.
I, too, wish there were better processes implemented to catch this type of activity with hosting providers and registrars.
Anonymous
Apr 26th 2016
8 years ago